An integral part of doing business in any company is the destruction of data. This is doubly true for modern companies who operate on-line and keep their data in a digital form, possibly on some server that is not even theirs.
A while ago data destruction was a straightforward process – you shredded the documents, and for extra security, did that one or two times more. However, these days, the process is more complex, not in the least aided by complex regulations and the simple fact that there is much more data to handle. With this, the chances for errors and misjudgment rise considerably.
Deletion vs Destruction
Deletion is a way of erasing data where the rewritable media remain re-usable, while the other two methods – degaussing and destruction – destroy the media in process. Obviously, the latter two methods are costlier, but they are deemed safer at the same time. Let’s take a closer look at all these methods.
Erasure
Data erasure is the simplest method and it’s the one most commonly used among regular folk in everyday life. It’s as simple as emptying the recycle bin on your desktop. However, there are certain caveats. In most cases, the data isn’t deleted immediately, but only marked for deletion: it will be overwritten when new data is saved on the hard disk. This means that such data can potentially be recovered easily, particularly if the hard drive isn’t used often.
This may be an appropriate method for really low-risk or inconsequential data, but such data cannot be considered as truly deleted. By ‘erasing’ data, we mean the use of special software solutions that will immediately overwrite the data marked for deletion, instead of waiting for new data to arrive and overwrite. The rationale for waiting is simple – there is a performance penalty associated with overwriting every time something is marked for deletion. But for risky data, you really have no choice.
Fortunately, there are plenty of free and, more importantly, open-source tools that can be used to perform this kind of data wiping. The operating principle of these tools is simple: they write the whole hard disk (or parts with data) with a string of zeroes, ones or a random string of characters. There are plenty of standards put in place by various government organizations, but one of the first and the most popular is the Gutmann Method, stipulating up to 35 overwrites.
In practice, however, with modern hard drives there is little benefit to overwriting more than three or four times as the encoding scheme they use is different, density is markedly higher and there is less volatility. The important thing is to perform a verification after the overwrite process to prove that data isn’t there anymore.
Drawbacks
This is not a foolproof method: disks may have bad sectors that cannot be written to, but from which pieces of data could still be recovered. Some hard disks incorrectly implement the safe erasure technologies that would ensure that even those sectors are overwritten.
Keep in mind that erasure simply doesn’t work for flash drives (this includes SSDs) due to the way they store data. Overwriting is possible, but one can never be certain that data has been fully destroyed, thanks to their wear leveling methods. (They’ll do the job just fine when it comes to corrupting data you really need, as per Murphy’s Law.) Physical destruction methods or crypto-shredding (see below) are your best bets. Or simply, avoid storing sensitive data on flash drives altogether.
In a nutshell, this method is reasonably safe for most applications, and it is also the most economical one, as the hard disks can be reused afterwards. However, you’re still relying on software, and things might go awry at any time. That’s why physical destruction methods are most secure and must be employed if you want to be 100 percent certain that the data will be destroyed.
Crypto-Shredding
Crypt-shredding is an alternative to data erasure (sanitizing) methods. It differs in that the data is not really deleted. Instead, what is deleted are the encryption keys. Without them, the data cannot be accessed – it looks a lot like random gibberish instead. Of course, it requires the implementation of encryption to be effective. All data written to the disk must be encrypted.
This method is useful for cloud-based systems, where you might not have total control over how your data is deleted. The best you can do then is to store encrypted data and delete the keys when it isn’t required anymore. That way, no one can access the data (at least in theory).
The method is as safe as the encryption method that is employed. The current strongest encryption methods seem safe, but it remains possible that in the future, they will be solved and trivial to break. But by then, the data might not be relevant at all. Keep in mind that some encryption methods (or means to obtain encryption keys, such as pseudorandom number generators) can have government-installed backdoors that make it trivial for them to access your data. This has not been proven as of yet, but it is a possibility.
Degaussing
Degaussing is a method used to wipe data from magnetic-based disks and drives. This includes VHS tapes, cassettes, reel tapes, floppy disks, and hard drives. Almost all but the latter can be re-used after degaussing. Most hard-drives will become unusable and there aren’t any cost-effective methods for repairing them, save for manufacturer-specific tools to which you are unlikely to have access too. The reason degaussers destroy the hard drive is that, along with data, they also remove servo firmware without which the hard disk cannot function, even though it is physically intact.
Degaussing permanently destroys data by altering the magnetic field of a magnetic storage media. Degaussers are specially constructed machines optimized for such purpose.
The NSA maintains an approved degausser list. By using one of those products properly, you can rest assured that your data has been removed. The throughput of many degaussers is high, and they can destroy large amounts of media, some up to 300 hard disks an hour, even more in case of tape-based storage. This makes it a very useful and effective method.
In fact, some US government organizations specify degaussing as the only method that should be used for the destruction of data, as physical destruction of the drive could still leave small pieces of tape from which pieces of data could, in theory, be read using forensics technology. However, there is nothing stopping you from physically destroying the drive as a full measure.
Destruction
This is the old-school method that is applicable to all forms of data, digital or paper-based. The premise is simple – smashing up those drives ought to make them unusable, right?
Well, yes, but only under some circumstances. While you couldn’t exactly connect them to your own PC, platters containing data or fragments of tape still exist somewhere in a landfill, and an unscrupulous individual, a company or a foreign agent could restore at least some of it using state-of-the-art methods.
You may have heard of embarrassing reports in the news about data from various contracts made by government agencies surfacing after being restored from an improperly destroyed hard drive. While occurrences like this are unlikely to occur particularly do you, you should never discount the possibility. Also, you could get fined if it is determined that the data has not been sufficiently destroyed.
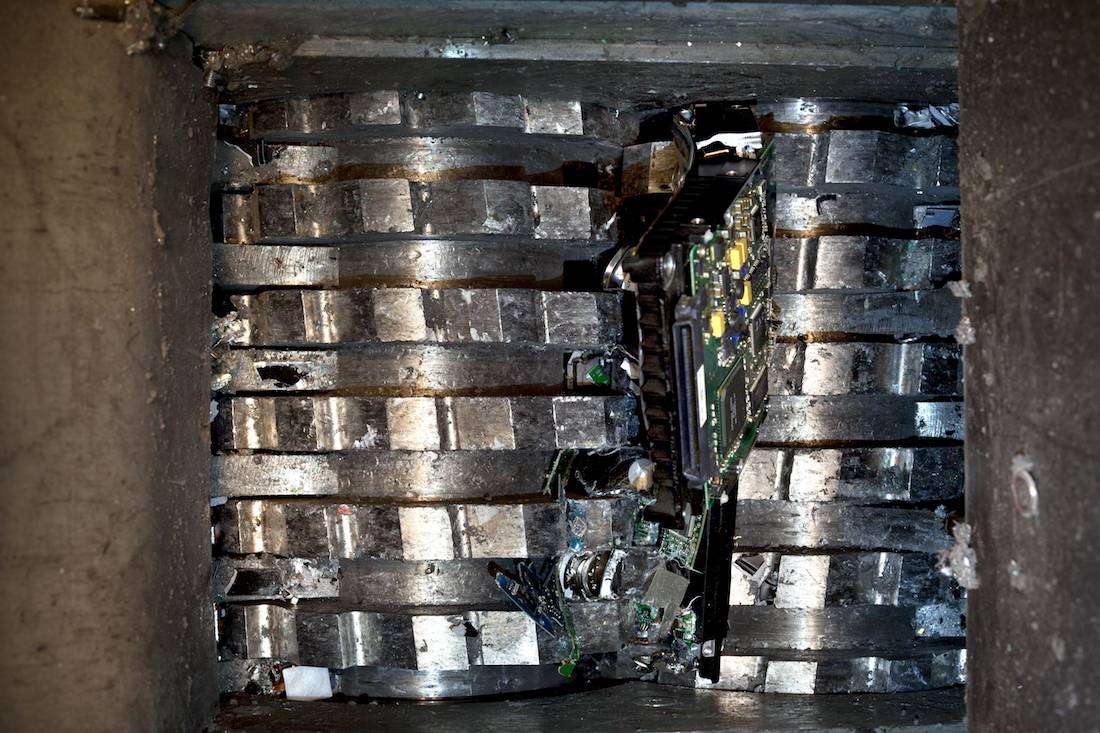
Just another day at the office.
How do you ensure that the data has been destroyed then? Well, the answer is as simple as the method. Shred them into as many pieces that are as tiny as possible. Mixing parts from as many devices as possible make any attempts at data restoration time-consuming and prohibitively expensive.
CDs, tapes and other devices can also be physically crushed and deformed. Incineration or chemicals can be employed, although such methods may not be the most ecologically viable.
Of course, you would have to contract specialized destruction companies for this, as the equipment is not something that is bought as part of everyday business operations. This in turn can present a security risk if you don’t trust the company.
However, the method is inexpensive and huge amounts of data can be destroyed at once.
Onsite vs Offsite
Both data destruction and storage are safer onsite than offsite, as they give you more control over the data in every step of the way. However, due to enticing prices of cloud storage and other technologies, data is being stored offsite more and more often. While some server services will provide you with a certificate of data destruction, many won’t. The most you can do if you feel uneasy about that is try not to use these services for the storage of sensitive data, even if they are certified.
When it comes to data destruction, most companies offer either onsite or offsite destruction. Onsite destruction is usually costlier, but may be required by law in some cases, so you would really have no choice but to comply. Regardless of the method, a good data erasure company will provide you with certificates of data destruction, as well as with detailed records of the process that you can employ to demonstrate compliance.
& The GDPR
The GDPR does not exactly prescribe the deletion method that is supposed to be used. But, it is heavily implied within the GDPR that a safe deletion mechanism should be used, mainly due to its provisions regarding security and safety by design and by default. It is more than reasonable to assume this also applies to data deletion. It also stresses the use of encryption and pseudonymisation, and as we’ve outlined above, encryption can be a handy tool for hassle-free deletion of data.
Also, do not forget the right of the data subjects (individuals) to be forgotten. This means you must cease all processing (except in rare circumstances) and delete their data. Depending on the severity of the data, you might need to utilize different methods – a simple erasure will do for non-critical data, while very sensitive data might require physical destruction of the media – a hard disk, usually.
Bear in mind that other national legislation might prescribe certain methods of data handling and deletion, so always try to be up to par with the current laws. Remember to be as transparent as possible and always keep record of your data deletion activities, especially sensitive and high-risk data. Good practices regarding data security can be ensured by adopting the ISO 27001:2013 standard, if your company can afford it.
It is much better to take the extra step than get slapped with a huge fine. If you are unsure as to whether the deletion you’re doing is safe enough, there are dedicated specialist companies that can do the deletion for you and issue official certificates. That way, even if something occurs, you can prove it’s not your fault.
Conclusion
While in most cases small companies won’t be required to take such drastic measures for data destruction, or at least not often, it is worth knowing about them should they become necessary. Remember that it may be safer and cheaper in the long run to invest in secure deletion than to risk losing sensitive data about your company, which could cost you much more, not even including lawsuits and fines if personal consumer data has been lost. Remember, hard drives can be replaced, but your reputation? Hardly.







